 Coming from a crisis management and business continuity background, I really enjoyed reading Enterprise-wide Risk Management: Strategies for linking risk and opportunity by DeLoach has a refreshing new approach to risk management that is is cross-functional, integrated and adaptable in the face of constant change, simply because traditional risk management approaches are no longer adequate in today’s rapidly changing world in where traditional risk management is too fragmented and function-driven.
Coming from a crisis management and business continuity background, I really enjoyed reading Enterprise-wide Risk Management: Strategies for linking risk and opportunity by DeLoach has a refreshing new approach to risk management that is is cross-functional, integrated and adaptable in the face of constant change, simply because traditional risk management approaches are no longer adequate in today’s rapidly changing world in where traditional risk management is too fragmented and function-driven.
The evolution of risk management
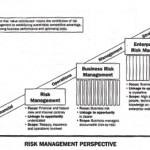 There are many excellent and self-explaining illustrations in this book, but the one that fascinated me the most is the one to the left, showing how enterprise-wide risk management is the perfection of risk management in business, enterprise risk management is seen as a natural evolution of operational risk management into a strategic process, with clear linkage to business opportunities, and with the purpose to align strategy, processes, people, technology and knowledge on an enterprise-wide basis.
There are many excellent and self-explaining illustrations in this book, but the one that fascinated me the most is the one to the left, showing how enterprise-wide risk management is the perfection of risk management in business, enterprise risk management is seen as a natural evolution of operational risk management into a strategic process, with clear linkage to business opportunities, and with the purpose to align strategy, processes, people, technology and knowledge on an enterprise-wide basis.
Four plus Two equals Six
Classic risk management literature acknowledges four ways of dealing with risk after establishing a risk matrix: Avoid, Reduce, Transfer and Retain or Accept. As it turns out, there are six ways, not just four ways to deal with risk. Two more are Exploit and Ignore. DeLoach points at exploit, while Tomlin (2006) points at Ignore, as I discuss in my later post on The six ways of dealing with Risk. And, ‘Exploit’ also makes into a discussion on risk management as a core competence by Lessard and Lucea (2009).
Reference
De Loach, J. W. (2000). Enterprise-wide Risk Management: Strategies for linking risk and opportunity. London: Financial Times/Prentice Hall.
Copyright note: The image used in this post is taken from the above book.
Author link
- linkedin.com: James W DeLoach
Buy this book
Related
- husdal.com: The six ways of dealing with risk
- husdal.com: Risk management as core competence