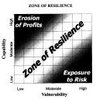
 Are you gambling with your supply network? You should be aware that the supply network is inherently vulnerable to disruption and the failure of any one element in it could cause the whole network to fail. Current trends call for a supply network design that is both secure and resilient; that means a supply network that has advanced security processes and procedures in place, while at the same time being resilient enough to respond to unexpected disruptions and restore normal supply network operations.
Are you gambling with your supply network? You should be aware that the supply network is inherently vulnerable to disruption and the failure of any one element in it could cause the whole network to fail. Current trends call for a supply network design that is both secure and resilient; that means a supply network that has advanced security processes and procedures in place, while at the same time being resilient enough to respond to unexpected disruptions and restore normal supply network operations.
In their article, “Building a secure and resilient supply chain“, James B. Rice and Federico Caniato point at a number of actions and responses to achieve supply chain resilience.
Security versus Resilience
A first step in creating a supply network that is both secure and resilient is to recognize that the two are not the same. This distinction becomes important when developing plans focuses on security and resilience respectively.
Actions to improve security can be classified into three categories:
– Physical security
– Information security
– Freight security
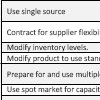
Actions to improve resilience can be be divided into
– Flexibility
– Redundancy
Flexibility
An important distinction between flexibility and redundancy is that the latter involves capacity that may or may not be used; it is this additional capacity that would be used to replace the capacity loss caused by a disruption. Flexibility, on the other hand, entails redeploying previously committed capacity.
The following table illustrates the advantages and disadvantages of actions in relation to
– Supply
– Transportation
– Production Facilities
– Communications
– Human Resources
Reference
Rice, J.B. and Caniato, F. (2003) Building a Secure and Resilient Supply Network. Supply Chain Management Review, Vol. 7, No. 5, pp. 22-30
Author links
- linkedin.com: James B Rice
- linkedin.com: Federico Caniato
Related
- husdal.com: Is Sheffi’s resilient enterprise the answer?